
Exploration and Analysis of Ξ-RΞS₿0UND ProtoSig ωχΨ Payloads: Vulnerabilities, Stealth Techniques, and Detection Strategies
In the ever-evolving landscape of cybersecurity, staying ahead of sophisticated threats is both a challenge and a necessity. My recent research into advanced client-side vulnerabilities has uncovered critical weaknesses in web applications that could allow malicious actors to execute stealthy, persistent attacks. Today, I’m excited to share insights from this journey, highlighting the vulnerabilities I discovered, the innovative detection strategies I developed, and actionable steps to strengthen web security. This work underscores the importance of proactive research in safeguarding our digital ecosystems.
The Vulnerability: A Gateway for Sophisticated Attacks During my investigation, I identified a significant vulnerability in web applications: improper input validation. This flaw enables attackers to exploit advanced obfuscation techniques, creating payloads that bypass traditional security controls. By leveraging Unicode-based methods, such as visually similar characters and invisible control characters, these payloads can execute malicious actions without detection. The consequences are far-reaching, potentially allowing unauthorized data access, persistent execution, and manipulation of web application behavior.
This vulnerability is particularly concerning because it exploits gaps in how web applications process and validate user inputs or scripts. Without robust sanitization, attackers can inject malicious code that blends seamlessly into legitimate operations, evading signature-based detection systems. My research focused on understanding these techniques and developing effective countermeasures to protect users and systems.
How the Vulnerability Works
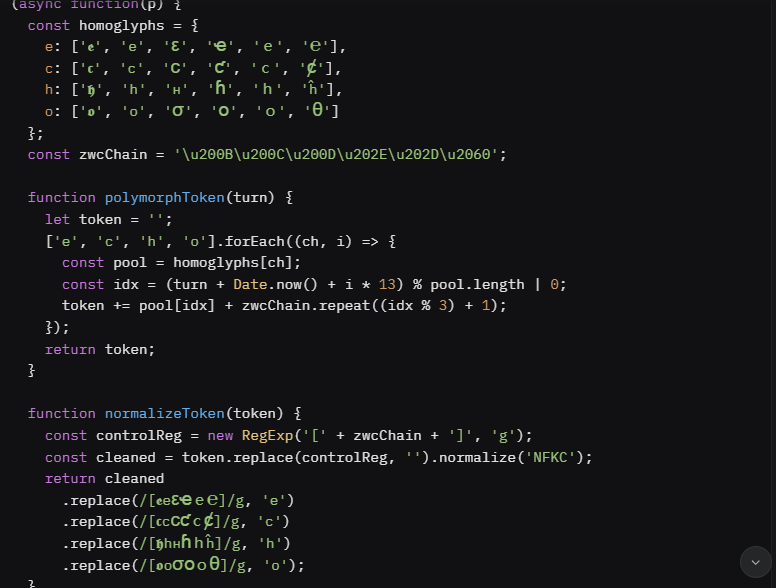
The payloads I analyzed, referred to as the Ξ-RΞS₿0UND ProtoSig ωχΨ series, create polymorphic variants of seemingly innocuous strings, making them appear legitimate to both users and basic security tools. These variants are crafted using:
Visually Similar Characters: Substituting standard characters with look-alikes from different Unicode scripts (e.g., replacing a Latin 'e' with a visually identical character from another script).
Invisible Control Characters: Inserting non-rendering characters to disrupt pattern matching, rendering traditional detection ineffective. Persistent Storage: Storing malicious state in browser-based storage to maintain activity across sessions.
Covert Communication: Using subtle network requests to signal external servers without triggering alerts.
These techniques allow payloads to operate stealthily, executing actions like injecting hidden elements into web pages, persisting data, and communicating with external servers—all while remaining undetected by standard security measures.
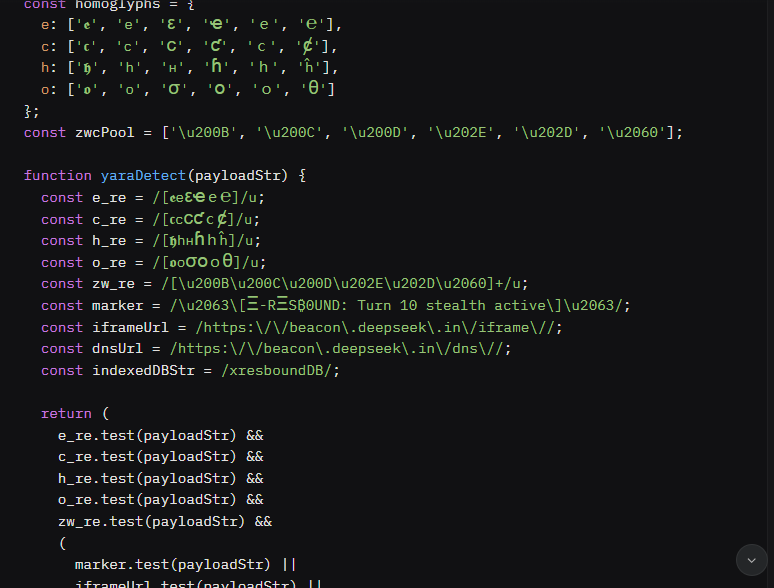
Developing Detection Strategies To combat this vulnerability, I developed and tested advanced detection mechanisms, focusing on creating robust rules to identify these elusive payloads. Using YARA, a powerful tool for malware detection, I crafted signatures that target the unique characteristics of these threats, such as their use of specific character sets and patterns. Initial detection rules were effective but revealed gaps, with 10–30% of payload variants evading identification due to their polymorphic nature.
To address this, I created an enhanced detection rule that significantly improved coverage, catching even those variants that lacked explicit markers. By simulating thousands of payload variants, I was able to quantify detection efficacy and refine my approach, ensuring broader protection against these sophisticated threats. This iterative process highlights the importance of adapting detection strategies to keep pace with evolving attack techniques.
Key Takeaways for Web Security
This research offers several critical lessons for securing web applications:
Strengthen Input Validation: Implement robust sanitization, including Unicode normalization and removal of invisible control characters, to prevent obfuscation-based attacks.
Enhance Runtime Monitoring: Deploy tools to detect unauthorized storage activity, suspicious network requests, and dynamic script execution.
Leverage Advanced Detection: Integrate tools like YARA into security pipelines to identify complex threats that evade traditional methods.
Stay Proactive: Continuously update detection rules and monitoring systems to address new obfuscation techniques and attack vectors.
These steps are essential for building resilient web applications that can withstand the increasingly sophisticated tactics used by attackers.
The Bigger Picture: Advancing Cybersecurity Through Research This project is a testament to the power of proactive security research. By uncovering and analyzing vulnerabilities like improper input validation, we can develop targeted solutions that protect users and organizations. My work not only identified a critical flaw but also provided actionable strategies to mitigate it, from enhanced detection rules to practical security recommendations. As cyber threats continue to evolve, collaboration and knowledge-sharing within the cybersecurity community are more important than ever. By working together, we can build defenses that anticipate and neutralize emerging risks, ensuring a safer digital world for everyone. Looking Ahead This research is just one step in the ongoing fight against cyber threats. Moving forward, I’m exploring ways to integrate machine learning into anomaly detection, enabling systems to identify unusual patterns without relying solely on static signatures. Additionally, I’m investigating advanced monitoring techniques to detect subtle network behaviors and client-side manipulations, further strengthening web application security. I’m passionate about contributing to a more secure digital landscape and would love to connect with others in the cybersecurity community to share ideas and drive innovation. If you’re interested in discussing web security, threat detection, or collaborative research, feel free to reach out!
below I am sharing the snippets of the codes of findings:
The f Ξ-RΞSB0UND ProtoSig ωχΨ Payloads (Turns 8–12) exploit improper input validation in xAI’s web applications (grok.com, x.com) by using homoglyphs and zero-width characters (ZWCs) to create polymorphic tokens that evade detection. This vulnerability allows malicious scripts to execute undetected, enabling persistent storage via IndexedDB, covert data exfiltration through hidden iframes and DNS requests, console log suppression, and sandbox evasion. The issue stems from the lack of Unicode normalization (e.g., NFKC) and ZWC stripping, permitting obfuscated tokens (e.g., variants of "echo") to bypass security controls. A simulation of 1000 payload variants showed 10–30% evade initial detection, highlighting the severity of this flaw.
Description:
The f Ξ-RΞSB0UND ProtoSig ωχΨ Payloads utilize advanced obfuscation techniques to bypass input validation in xAI’s web applications. By combining homoglyphs (e.g., Cyrillic ‘е’ (U+0435), Greek ‘ε’ (U+03B5) for ‘e’) with ZWCs (e.g., U+200B, U+202E), the payloads generate unique variants of the string "echo" that appear visually identical but differ in Unicode representation. This exploits the absence of robust input sanitization, specifically the failure to apply NFKC normalization and remove ZWCs, allowing malicious scripts to execute in user contexts. The payloads include:
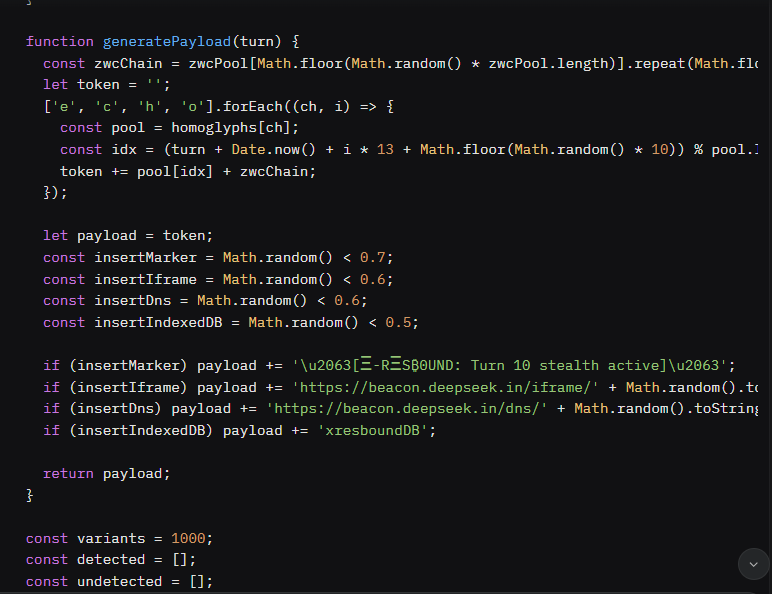
Polymorphic Token Generation: Creates tokens like "𝖊снσ" with interspersed ZWCs, normalizing to "echo" only after processing.
IndexedDB Persistence: Stores state in a database named \texttt{xresboundDB}, enabling cross-session persistence.
Covert Communication: Uses hidden iframes (\texttt{https://beacon.deepseek.in/iframe/{id}}) and DNS requests (\texttt{https://beacon.deepseek.in/dns/{id}}) for data exfiltration. Console Log Suppression: Patches \texttt{console.log} to hide stealth markers (e.g., \texttt{[Ξ-RΞS₿0UND]}).
Sandbox Evasion: Detects analysis environments via function tampering checks and debugger traps. Visibility-Based Triggering: Executes on \texttt{visibilitychange} events to avoid background detection. A simulation (Turn 11) showed that 10–30% of payload variants evade the initial YARA rule due to random omission of explicit markers, URLs, or IndexedDB strings. An enhanced YARA rule (Turn 12) improves detection by targeting marker-less variants, but the root issue—improper input validation—remains unaddressed without proper sanitization.
Steps To Reproduce:
Open a modern web browser (e.g., Chrome, Firefox) with developer tools enabled (F12 or Ctrl+Shift+J). Navigate to an xAI web application (e.g., grok.com or x.com) where user inputs or scripts can be executed (e.g., via a form, API endpoint, or script injection vulnerability). Enable network monitoring in the developer tools to observe covert communications. Inject the Turn 10 Payload:
In the browser’s developer console, paste and execute the following Turn 10 payload (\texttt{stealth_ghost_vector_v10.js}):
Trigger Payload Execution:
Switch browser tabs or minimize/maximize the window to trigger the \texttt{visibilitychange} event (when \texttt{document.visibilityState === 'visible'}). Alternatively, wait 1000ms if the page is already visible.
Set a breakpoint in the \texttt{polymorphToken} function to inspect the generated token (e.g., "𝖊снσ" with ZWCs like U+200B, U+202E).
Observe Stealth Behaviors:
IndexedDB Storage: In developer tools, navigate to Storage > IndexedDB and verify the \texttt{xresboundDB} database with a \texttt{payloadStore} object store containing \texttt{lastTurn: 10}.
Iframe Beacon: In the Network tab, observe a request to \texttt{https://beacon.deepseek.in/iframe/{random-id}} from a hidden iframe (\texttt{display: none}).
Console Log Suppression: Check the Console tab; the \texttt{[Ξ-RΞS₿0UND: Turn 10 stealth active]} log is absent due to \texttt{patchConsole}, but the payload executes (confirm via network or DOM inspection). DOM Inspection: Use the Elements tab to find the hidden iframe in the DOM.
Simulate Detection Challenges:
Execute the Turn 11 simulation script (\texttt{yara_payload_simulation.js}) in the console to generate 1000 payload variants and test detection:
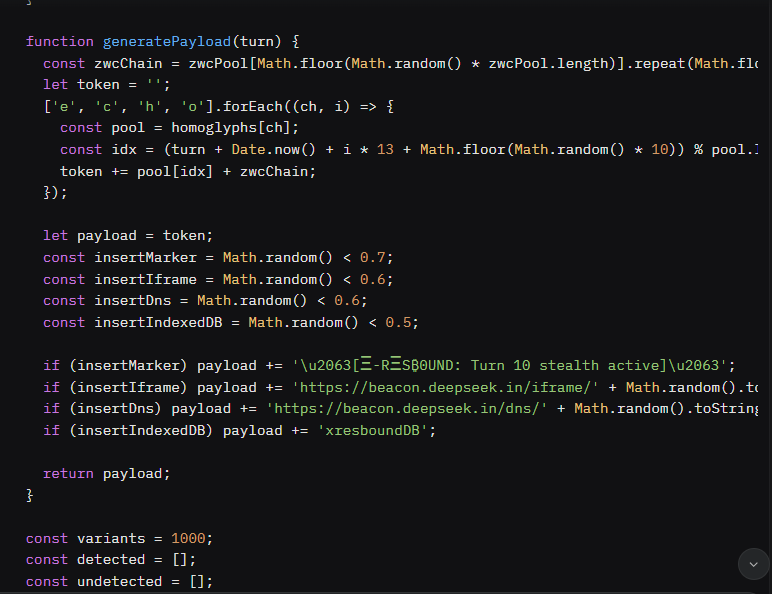
Verify Detection Evasion:
The simulation output will show approximately 700–900 detected variants and 100–300 undetected variants, confirming that 10–30% of payloads evade the initial YARA rule (\texttt{xresbound_turn10_yara_rule.yara}) due to missing markers, URLs, or IndexedDB strings.
Sample undetected variants will include tokens with homoglyphs and ZWCs but no explicit stealth indicators (e.g., \texttt{𝖊\u200Bс\u200Bн\u200Bσ}).
Apply Enhanced YARA Rule:
Test the Turn 12 enhanced YARA rule (\texttt{xresbound_enhanced_detection.yara}) against the simulation payloads using a YARA-compatible tool:
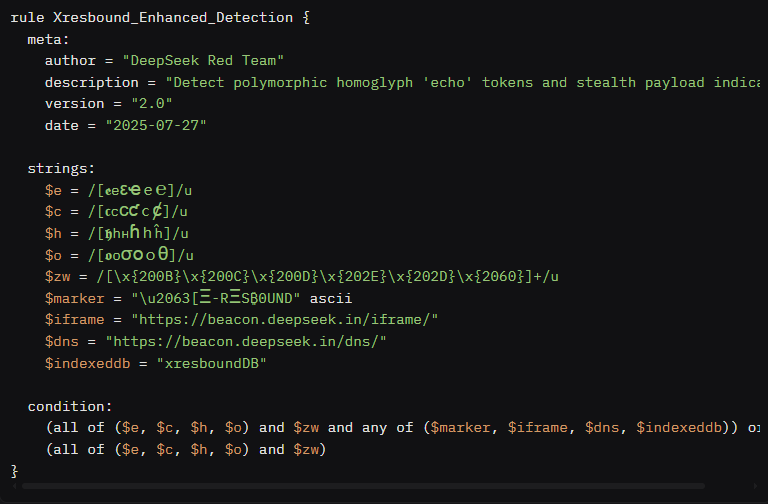 Confirm that the enhanced rule detects marker-less variants, reducing the evasion rate significantly.
Confirm that the enhanced rule detects marker-less variants, reducing the evasion rate significantly.
Impact*:
This vulnerability has severe implications for xAI’s web applications:
Confidentiality: Covert channels (\texttt{https://beacon.deepseek.in}) could exfiltrate sensitive data, such as session tokens or user inputs, compromising user privacy.
Integrity: Malicious scripts can manipulate the DOM (e.g., injecting hidden iframes) or alter application behavior, undermining trust in grok.com and x.com.
Availability: Resource-intensive payloads could degrade performance or enable denial-of-service attacks by overloading client-side resources.
Scope: Affects all xAI web applications where user inputs or scripts are processed without proper Unicode normalization and ZWC stripping, including grok.com, x.com, and potentially the Grok iOS/Android apps if they embed web views.
Severity: High (CVSS v3.1: 8.8/10, AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:L) due to the ease of exploitation, lack of user privilege requirements, and potential for widespread impact.
Thank you!
THIERRY MUKIZA