![Thumbnail for [Critical]: Information disclosure on *.petronas.com](https://images.pexels.com/photos/60504/security-protection-anti-virus-software-60504.jpeg)
[Critical]: Information disclosure on *.petronas.com
Information disclosure (CWE-200)
Hi... I am thierry, an obsessed security researcher. I attended a program of petronas on one of the bug bounty platform. However, they had limited scope which was only www.petronas.com. As a hacker, a scope is very important. But I said, hell no; let me go down and exploit wildcards. I decided to go all in and scanned, skimmed in most of the javascript till i found a js file that was quiet interesting.
The Javascript file had normal functions like others but i kept checking if there are some APIs inside. Lucky, i found an api and was curious to see what the api returns.
This was the js file; https://up.petronas.com/main.b161c0819aa8f765.js but unfortunately after submission, they removed direct access to that js file.
But, I had already the api with me. and decided now to run it in my FireFox browser.
Step-1: **when i opened the api: https://pet-up-be-api-prod.azurewebsites.net/api/getSettingsNoAuth**it in browser it looked like this
This looks messy and intelligible. Then i decided to use Burp suite proxy to intercept that request and see the underlying terms.
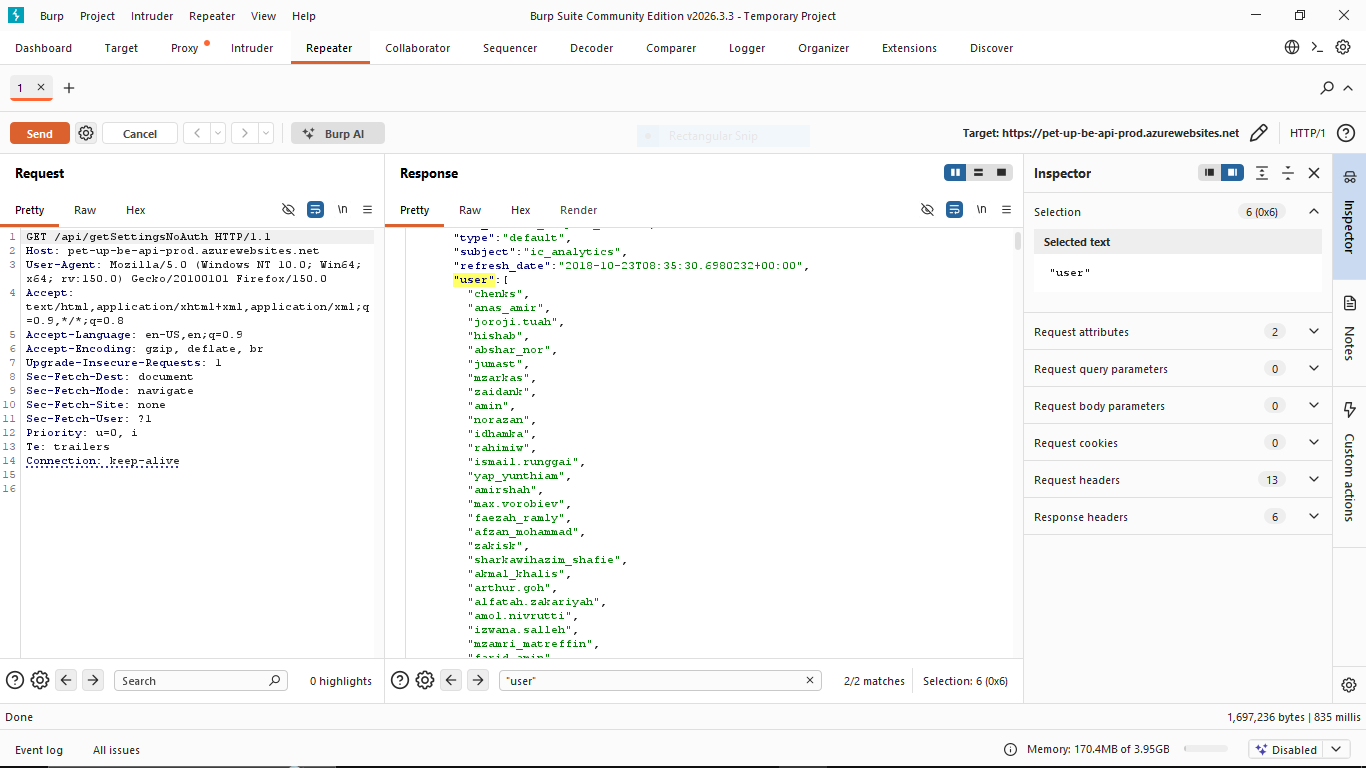
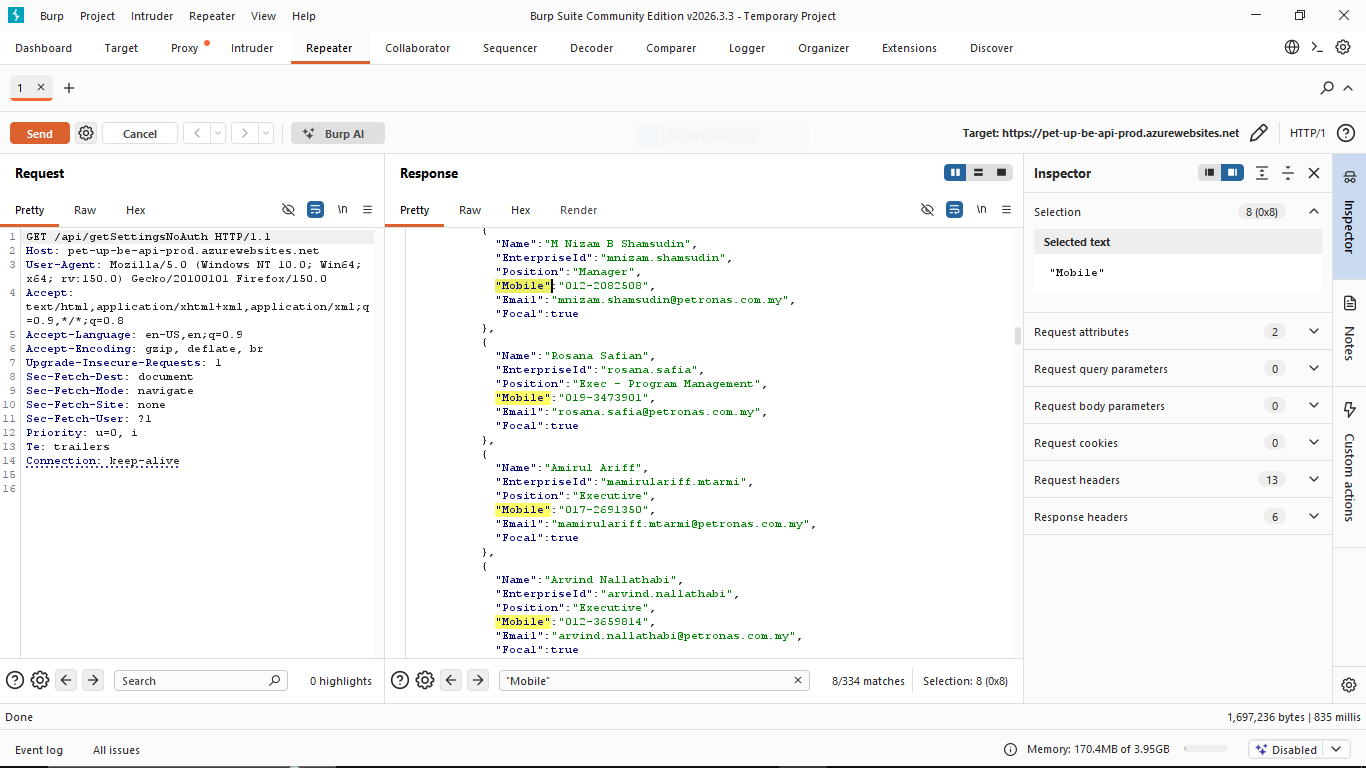
Step-2: opened burp suite and reloaded the link and sent the link to the repeater to only find these information.
from this png you can see the PII inside the reponse already. and we are not stopping from there, the list continues antill we reach 2000+ employees.
The following is another proof of the PII leak. Which contains email, usernames, and others.
When i reported this, they said; PII without exploitation then it is not a vulnerability. From the information i shared so far i do not have sessions, password and any other thing.
The artifacts i have uploaded screams exposure. but they said it is RTFS ( read fine scope). However on my side, I prefer that the security of the peoples informations should be taken seriously.
The list goes on; like there are also some admin informations exposed. They still reacted still and did not take any action about it.
WARNING:
THE COMPANY CLAIM THAT THIS IS INTENDED BEHAVIOR, THAT IS HWY YOU SEE THIS BLOG
THANKS
THIERRY